After watching one too many movies where a “cabin” has 20′ windows, a wine cellar, soaking tub, rainforest shower and a room that could be called a “foyer,” I have made a simple checklist. You’re welcome, Hollywood.
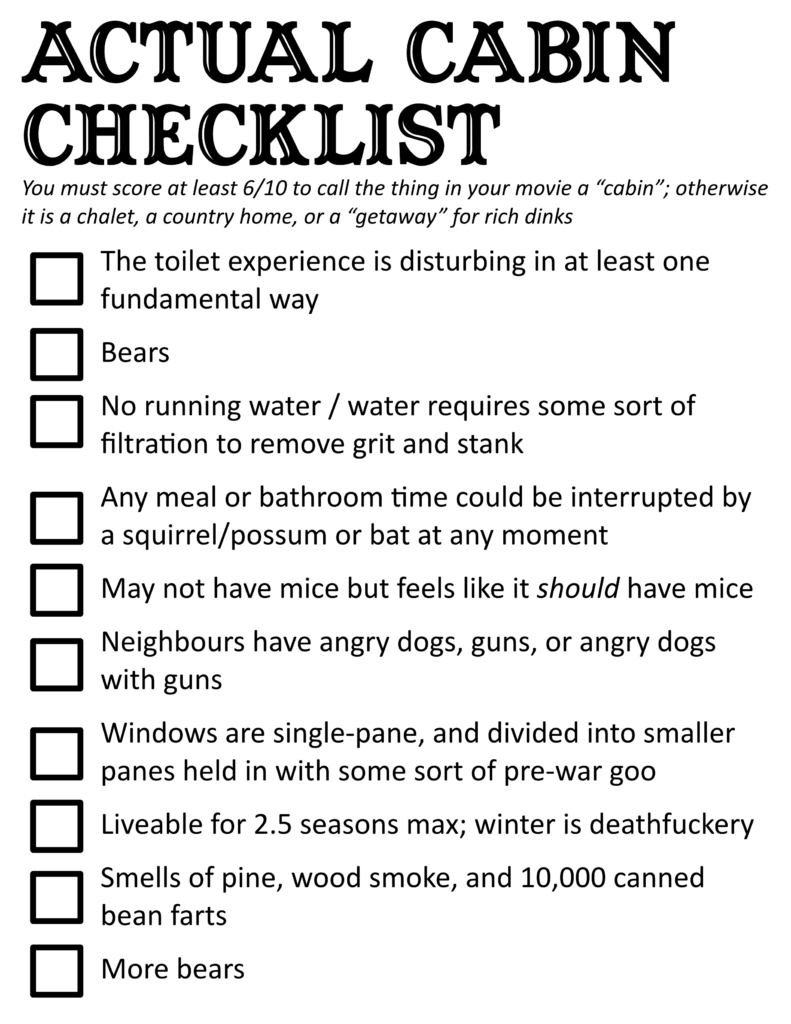
After watching one too many movies where a “cabin” has 20′ windows, a wine cellar, soaking tub, rainforest shower and a room that could be called a “foyer,” I have made a simple checklist. You’re welcome, Hollywood.
Watch this video and get back to me and let’s talk about the genius of the zag. Yes, there’ll be a test.
Tim Minchin is, of course, a brilliant man. I am not Australian and have never been to Australia and in all likelihood will never visit Australia but White Wine in the Sun is one of only two Christmas songs that makes me cry. 1The other one is the Cat Carol by Meryn Cadell, which frankly qualifies as goddamn trauma.
I am coming this two years too late, having seen Minchin’s speech at the Art of Tax Reform summit, itself a work of art.
Play it Safe is epochal for me on a number of levels.
First, it’s the perfect response to a mundane marketing request. “Say the usual things about creativity and the arts and uniqueness and vision,” goes the ask.
“How about I do exactly the other thing: champion safety and mundanity verbally, juxapose it visually, and do this knowing that it will land, because I trust my audience.”
And by Jiminy, does it land.
Partly because Minchin is a once-in-a-lifetime songwriter: he knows music, he knows lyrics, he understands the interplay.
Partly because the cultural context of the project — which he also fully understands — can underpin the zag of the zig. You can talk about the iconic Opera House in a “play it safe” context because you know that everyone knows that it wasn’t a “safe” project.
What am I taking away from Play it Safe today, which I think everyone should take away from it?
This isn’t just a Minchin thing; it’s why Sinners why was a box-office shattering surprise in an era of cookie-cutter IP products, it’s why Peacemaker has resurrected the careers of Z-tier glam metal bands through artfully deployed opening-credit dance numbers.
Trust. Context. Fun.
Pure magic.
And — if you have 13-odd minutes to spare — the address to the Tax Reform Summit is also well worth your time. It starts as an articulate dissection of the creative process, and winds up of being a repudiation of AI slop, small-minded conservative budgets, and a whole-throated confirmation that big ideas, and big risks taken on culture can have incredible long-term rewards; much more than the “safe” bets ever do.
You’ll see Play It Safe again in that presentation, but it’s worth a second look. Trust me.
Australia, I’m jealous. Where’s Canada’s Tim Minchin? We need him, or her, or them.
Tip for AI adherents: if you want people to use it, make it less cancerous.
I was on a board call last week where one of the board members was using read.ai to transcribe minutes. To read the minutes, I had to make a read.ai account.
Sure, whatever. So I made an account with my Google account.
Today, I log into an entirely different meeting with an entirely different person. Not signing in with Google at all.
You’ll never guess what happens. Via cookies in my browser, read.ai determines that I’m a Google user, and auto-injects itself — without permission, and without asking — to “transcribe” the meeting.
After the meeting, I get a note asking why I’d added an AI bot to the call. I hadn’t. I’m baffled.
It takes me — a reasonably competent person, with fairly good technical skills — 45 minutes to figure out what’s going on. That this venomous little company is creeping around my browser to creep into my calls with no explicit prompts or permissions.
Another straw on the camel’s back of AI being — from an end-user perspective — an intrusive, unhelpful, rapacious way to kill the environment and add absolutely nothing of value to our lives.
I’ve gone from being AI-curious a few years ago to viewing it as an actively negative force in my life. Every interaction with technology now comes with effort and debt to turn off unwanted “features,” bloatware, waste.
Nobody wants this. Nobody needs it. I pray, daily, that Ed Zitron is right and this fever dream bubble is about to collapse.

A vague developing thought on image-generation LLMs: used to be with image banks etc that you’d have to find a metaphor that worked and apply it, creating a layer that made readers think a little differently about the piece. Not everything — “senior looks baffled by technology” stock photos will always be with us — but broad writing would often be paired with conceptual visuals.
You’d sift through some banks and look for something that makes connective sense, but isn’t literally the headline regurgitated as a vaguely Ghibliesque picture. Or, saints be praised, hire and work with an artist who brings an intelligent interpretation to the piece.
You’re writing something on, I don’t know, inheritance tax. How do you show the positive or negative (depending on your slant) of this? To the image bank, or ask an artist for help: you might not be thinking of “large fish eats smaller fish” or “the old piggy banks where the hand grabs the coin” but once you see them, you think “oh, that’s an interesting way to look at this” and you’re off to the races. You’re forced into a metaphorhical framework.
Now that you can generate literal slop (both meanings of literal) to illustrate. Type “inheritance tax is bad” into an AI image generator and you get this kind of good-enough shiny horseshit, which adds no value to the overall piece, it’s just confirmatory noise (and eerily close to the “senior baffled by technology” trope:

We’re losing a layer of metaphor:substance in illustrated pieces in favour of literal:literal, and I think that ultimately makes the reading and thinking components just a little bit worse.
The list of resources for local residents on this site continues to grow with a new page on newsletters you can subscribe to from local community organizations and businesses.
Also added to the Kingston drop-down menu.
I continue to be fascinated — maybe uniquely so? — by puffery. Probably because of the marketing background, but the notion that being untruthful is okay if the lie is extravagant enough that a layperson wouldn’t believe it 1my own words; I’m working on a set of definitions in case law, which will be interesting (to me, anyway). is not only intriguing, but I’d argue in some ways necessary to modern advertising.
At the far end, it makes perfect sense. If you watch an ad for Skittles and a unicorn touches a couch with its horn and the couch turns to Skittles, it would be preposterous for somebody to sue the Skittles people if a furniture-transforming unicorn fails to appear when they open a pack.
But at the other end of the spectrum, there’s a line past which the grey starts shading into black, and judges are making very nuanced decisions based on, I’d argue, very little guidance. Looking at CanLII, the word ‘puffery’ has been used a lot in court decisions in the last few years, with subtypes of puffery including…
Nothing substantial here today, but a bit of a placeholder to remind myself that I’d like to unpack this a bit more.

This is part eleven of a multi-part series reviewing Canada’s Anti-Spam Legislation in practice since its introduction in 2014 and the beginnings of enforcement in 2015. Crosslinks will be added as new parts go up.
Part 4: Case File – Compu-Finder
Part 5: Case File Anthology, 2015-2016
Part 6: Case File – Blackstone Education
Part 7: Case File Anthology, 2017-2018
Part 8: Case File – Brian Conley/nCrowd
Part 9: Case File Anthology, 2019-2022
Core resources:
Enforcement Actions Table (CASL selected)
I’ve been taking various runs at a wrap-up of almost 10 years of CASL being on the books, and keep kind of bouncing off this summary. In part because it’s hard for me – as somebody who needs to interpret the regime, but who is also interested in looking at its effects over time – to get a firm grip on how it is implemented and practised based on the last 9-and-a-bit years of enforcement.
I’m going to break this down into a few components:
CASL isn’t just for “spam”. Frankly, they should rename it. “Anti-Spam legislation” is a snappy phrase but causes more confusion than is warranted. The conventional understanding of spam is junk email, but this legislation applies to texts, intrusive software (malware), browser extensions… essentially, if it’s delivered digitally, it falls into the remit.
ALL Commercial Electronic Messages (CEMs) are prohibited. By default. Assume any commercial message is not allowed to be sent, and CASL carves out exceptions to the general prohibition.
ANY CEM contaminates a non-CEM. Even if a message is 99% non-commercial, any inclusion of any content that – from the Act:
having regard to the content of the message, the hyperlinks in the message to content on a website or other database, or the contact information contained in the message, it would be reasonable to conclude has as its purpose, or one of its purposes, to encourage participation in a commercial activity, including an electronic message that
(a) offers to purchase, sell, barter or lease a product, goods, a service, land or an interest or right in land;
(b) offers to provide a business, investment or gaming opportunity;
(c) advertises or promotes anything referred to in paragraph (a) or (b); or
(d) promotes a person, including the public image of a person, as being a person who does anything referred to in any of paragraphs (a) to (c), or who intends to do so.
The Act, 1(2)
Requests for consent are also CEMs per s1.3 of the Act. This results in a Catch-22 – you can’t market without permission, but asking for permission is marketing. Added value is therefore key – or couching a consent request in an otherwise legitimate communication. I can’t email you out of the blue (except under a certain set of circumstances) asking you to opt into my newsletter, but I can post on LinkedIn telling people I’ve created a free white paper on best practices in Z, and require people to sign up for my newsletter to download that white paper.
From Compu-Finder:
From Porter Airlines:
From Blackstone:
From Ghassan Halazon:
From 514-Billets:
From Datablocks/Sunlight Media:
From Brian Conley / nCrowd:
From Orcus Technologies:
From Scott William Brewer:
Who wants spreadsheets? We got spreadsheets.
Wuxtry! Wuxtry! Getcher spreadsheet heah!
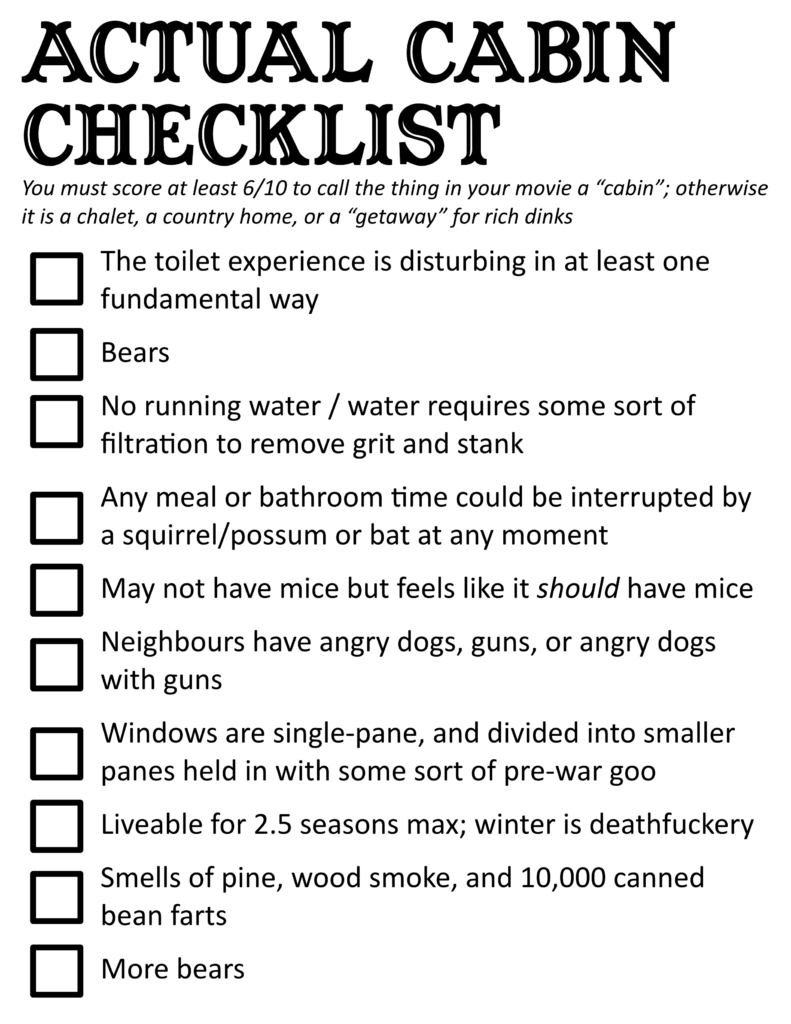
When I tabulate all issued penalties from decisions to date, I arrive at $3,163,000. Imposed penalties – admittedly with fuzzy math around coupon redemption rates for the 514-BILLETS issue – come in at $1,185,750.
The differential is $1,977,250 – about 63% of issued penalties wound up not being imposed. We’re also assuming that all imposed penalties were, in fact, paid – in several cases the companies that had imposed penalties then seem to have gone out of business, so the likelihood of the Canadian Government having seen that money is dim.
I also can’t account for about $500,000 that CRTC summaries say were imposed; more on that under “CASL as a marketing exercise,” below.
This kept running through my head as I tried to look at decisions and figure out if there was any clear logic to an external user regarding:
As somebody raised in the church, the more I poked at it the more I felt I understood the terror of the, I don’t know, Hittites: there’s a baseline set of behaviours you’re expected to follow, but it’s impossible to know when the eye of judgment will fall upon you, and when it does, there’s no real way to predict the extent of your punishment.
Beyond those examples, it’s hard to know how evenly the law is applied – or even what the specific triggers and determinants of a penalty are. It doesn’t feel entirely random, but since most decisions are posted without the number of campaigns or scope of sends, there’s no way to draw a line from the violation to the penalty in a way that makes sense in terms of whether it’s being evenly applied.
The other thing is that the pattern of CASL actions – from the perspective of somebody that works in marketing – seems to be more about creating the impression of enforcement than consistently and rigorously applied penalties.
The most recent snapshot contained the following now-familiar text:
Payments and Penalties Under CASL
Since CASL came into force in 2014, compliance and enforcement efforts have resulted in administrative monetary penalties and undertakings totalling over $3.6 million.
I can’t account for these numbers: even the $3.6 million is $0.5M higher than a manual tally of NOVs from the CRTC site (I’ve made a spreadsheet).
My own numbers land at $3,163,000 in issued penalties, but only $1,185,750 in imposed penalties – about 37% of the issued penalties wound up being actually imposed.1The imposed penalties number does include a bit of my own math, as the 514-BILLETS case resulted in the issuing of $75,000 worth of rebates, which I calculated at far less than that value in terms of what the ultimate cost to the company would have been.
But there’s also a pattern of big shock-and-awe announcements that get quietly walked back after the fact, or that lead to follow-on penalties much smaller than the initial ones:
A journey through CRTC CASL “Snapshots” show a pattern of reporting actions that weren’t actually taken under CASL – things done by the CRTC as a whole, but as far as I can tell unrelated to CASL or its enforcement.
For instance, in the most recent snapshot, headlines include:
In the previous snapshot, the headlines are all about various CRTC activities – a CRTC decision regarding botnet blocking (its development being the sole headline of an earlier snapshot), a report on a Canadian “dark web marketplace” (actually a reference to the previous snapshot, and not new news) and vigilance over malware called QAKBOT.
And so on. I won’t blow-by-blow this, but if you go back through the snapshots, the bulk of reporting isn’t actually about CASL, but other CRTC activities.
This makes perfect sense from a certain perspective. If you’re a parent, or a teacher, or have ever run a volunteer organization, there are times when you have a rule that you can’t practically enforce, and for whatever reason the common good isn’t enough to get people to follow it. Telling people there is a rule, and enforcing it sporadically, but with harsh enough penalties that it scares everyone into compliance, makes a lot of sense.
Starting with the assumption that the CASL team is smart, works hard, and is just not adequately staffed to provide perfect enforcement nationally at all times (which would take a preposterous scaling-up), big penalty announcements with quiet walkbacks, trumpeting non-CASL achievements in a way that makes CASL look vast and vigorous, is a good move. In the day to day, risks of getting caught are relatively low (see below), but when $1M+ penalties are making the headlines, the idea of getting caught in that net is scary.
But is scary enough?
Back when I started this analysis, I said my interests were:
What have we learned?
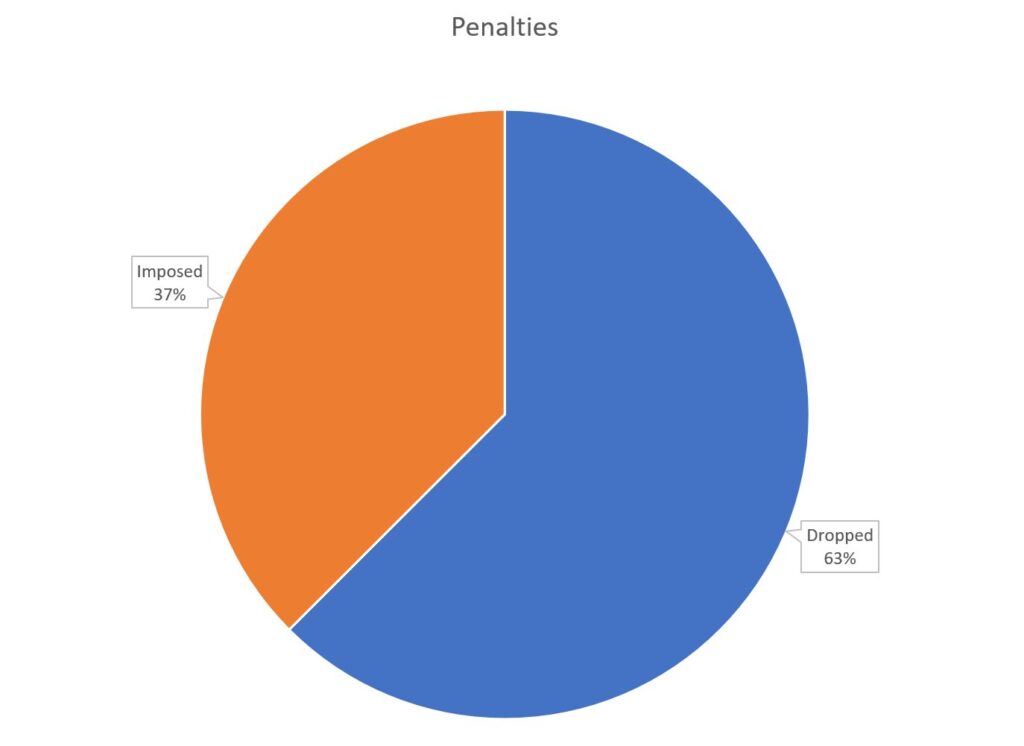
On the first front, the answer is clearly that complaints are not going down.
Arguably there are many reasons for this – including CASL’s own effectiveness in sensitizing the public to spam and fraud, driving reporting numbers up.
But – given the sporadic nature of enforcement, and the amount of fuzziness around what CASL is claiming, both in terms of penalties and its own vs. taking credit for other CRTC activity in its snapshot – I don’t have a great feeling about it.
Maybe it can’t “work”. Maybe the digital world is too big, and too global, and evolving too fast, for us to “beat” online fraud in any meaningful and lasting way, and stemming the tide is the best we can ever hope for. I don’t have the time or resources to really meaningfully compare CASL to other national spam protection regimes, so there aren’t any comparators out there I can easily index against.
It’s possible that looking at CASL through the same lens as other public-service organizations and criteria – is crime going down, as a measure of police effectiveness; wellness and death rates, as a measure of public health effectiveness – is a fool’s errand.
This leaves me with an aggregate shrug. Does CASL work? Shrug. Could it be doing better? For sure. Should we, as a society, allocate the kinds of resources to it that it would take to do better? Shrug.
But if my read of CASL actions, and their own snapshot headlines, is correct and the slow pivot is from enforcement to awareness, and there’s been a general slide from “we can stop this” to “our best chance is to educate the public, focus only on the worst offenders, and rely on private enterprise to develop better detection and protection algorithms,” that’s a big change over the last 10 years that’s never been explicitly acknowledged.
Low. Like, real low. The math remains 218,465 complaints per eventual financial penalty. The “lowest” threshold of effort CASL imposes, a notice to produce, still only happens once per 1000 complaints. That’s not a threshold, I’m not saying “nothing happens until you get to 1000 complaints,” that’s just how it averages out.
But, as detailed in the “Old Testament” section above, also horrifyingly arbitrary.
I am not a lawyer and this is not legal advice, but if I were to get one takeaway from all of this, it’s really a two-part maxim:
If I step back and squint and try to make sense of this decade of decisions, the pattern that seems to come through the fog is that getting CASL to focus on you is rare, and best-effort attempts to follow the rules seem to buy a lot of, if not absolute, forgiveness.
CASL decisions tend to land on unequivocal wrongs. There’s not a lot of stuff in the archives that suggests that they penalize innocent mistakes, or even grey-area decisions. There’s never been a decision that has come down on a public service organization, charity, or non-profit. Not to say there won’t ever be, but the focus seems to be on parties that are clearly doing wrong, should have known better, and did scammy, spammy things anyway.
Don’t break the law! Never break the law!
In principle, CASL is a good thing. It’s reasonably clear. We would all live in a better world if everyone followed these rules. So we should.
But… if you make an inadvertent mistake, or you look back at a campaign and say “oh, we should have done X,” or “I don’t know if we were in full compliance with Y,” I wouldn’t let it ruin your lunch. Learn, pull up your socks, and do better on the next one.
With text-based phishing and malware and online casinos and a whole planet of scammers, the top-of-mind analogy is the city’s on fire and there are riots in the streets. Jaywalking is still wrong, but if you forget to check the traffic lights at 2 a.m., you’re not the kind of problem the CRTC is looking for.
I didn’t mean for this to hit 3,000 words! I’ll stop here.
Next up, stepping a bit outside the review mandate, but bringing it back to my own interests: poking at whether or not students and academic institutions can be considered to be in a “business relationship,” which has a heavy impact on CASL but a lot of other things too. This might take a while. Expect more quick observations on IP, privacy and marketing in the interim while I chip away.
This is part ten of a multi-part series reviewing Canada’s Anti-Spam Legislation in practice since its introduction in 2014 and the beginnings of enforcement in 2015. Crosslinks will be added as new parts go up.
Part 4: Case File – Compu-Finder
Part 5: Case File Anthology, 2015-2016
Part 6: Case File – Blackstone Education
Part 7: Case File Anthology, 2017-2018
Part 8: Case File – Brian Conley/nCrowd
Part 9: Case File Anthology, 2019-2022
Core resources:
Enforcement Actions Table (CASL selected)
A quick late 2023 update: the CRTC has published an NOV for Sami Medouini for what appears to be text-based phishing campaigns; NOV below:
File No.: 9110-2021-00606
To: Sami Medouni
Issue Date of Notice: 11 July 2023
Summary of investigation
The Canadian Radio-television and Telecommunications Commission (CRTC) is responsible for the administration of sections 6 to 46 of Canada’s Anti-Spam Legislation (the Act), and the Electronic Commerce Enforcement (ECE) division of the Commission investigates potential violations pursuant to the Act.
In March 2021, CRTC staff launched an investigation into a series of high-volume phishing campaigns and potential violations of paragraph 6(1)(a) of the Act.
Paragraph 6(1)(a) of the Act states that it is prohibited to send or cause or permit to be sent to an electronic address a commercial electronic message (CEM) unless the person to whom the message is sent has consented to receiving it, whether the consent is express or implied.
Pursuant to section 22 of the Act, a notice of violation has been served on Sami Medouni for committing six violations of paragraph 6(1)(a) of the Act.
Between 22 December 2020 and 14 January 2021, Sami Medouni sent or caused or permitted to be sent at least 31,925 phishing Commercial Electronic Messages (CEMs) without the consent of recipients, from fraudulently obtained telephone numbers.
Specifically, Sami Medouni sent the following commercial electronic messages without express or implied consent by using six different telephone numbers:
In accordance with section 13 of the Act1Section 13 – Burden of proof: A person who alleges that they have consent to do an act that would otherwise be prohibited under any of sections 6 to 8 has the onus of proving it., the person who sends a CEM has the onus of proving that consent was obtained. There was no evidence obtained during the investigation to indicate that Sami Medouni obtained the necessary consent to send CEMs.
Information and evidence to support this investigation were gathered from multiple sources, including Notices to Produce pursuant to section 17 of the Act, and provided reasonable grounds to believe that, by using six separate phone numbers, Sami Medouni sent 31,925 CEMs without consent, representing six violations of paragraph 6(1)(a) of the Act.
Based on the information gathered in the investigation, the Director of the Electronic Commerce Enforcement division has issued a Notice of Violation, imposing an administrative monetary penalty of $40,000 to Sami Medouni.
Violations are connected to the number of phone numbers used — a “campaign” is a violation, not an individual message, so if Medouni allegedly bought a phone and used it to send CEMs until there were enough spam reports for carriers to block it, each phone would therefore represent a “campaign”. Ergo: six campaigns, comprised of 31K messages.
These are identified as phishing messages in the NOV itself; the CASL violation is strictly consent, but phishing is fraud under s380(1) of the Criminal Code. Unlike with Orcus, the CRTC does not mention investigations or criminal charges here.
This is only an NOV — I’ll update my overall stats when time allows, but this doesn’t change the math on final decisions (the differential between issued and imposed penalties is of interest, but I can’t update it until we get to the “imposed” part.
We’ll stay tuned on this, and move on to our wrap-up.
This is part nine of a multi-part series reviewing Canada’s Anti-Spam Legislation in practice since its introduction in 2014 and the beginnings of enforcement in 2015. Crosslinks will be added as new parts go up.
Part 1: Terminology
Part 4: Case File – Compu-Finder
Part 5: Case File Anthology, 2015-2016
Part 6: Case File – Blackstone Education
Part 7: Case File Anthology, 2017-2018
Part 8: Case File – Brian Conley/nCrowd
Part 9: Case File Anthology, 2019-2022
Core resources:
Enforcement Actions Table (CASL selected)
December 12, 2019
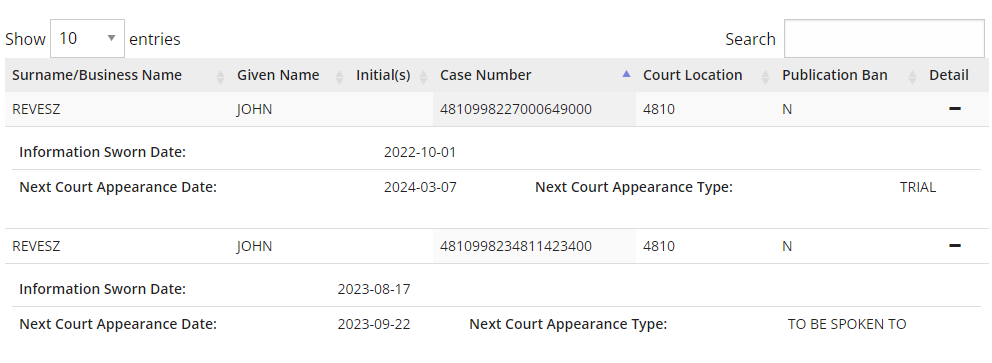
A $115,000 AMP issued for violations of s9 of CASL against John Paul Revesz and Vincent Leo Griebel, partners, Orcus Technologies.
This is one of the rarer cases of malware under CASL; in this case the Orcus Remote Administration Tool (RAT) found by the CRTC’s Chief Compliance and Enforcement Officer to be a remote access trojan, a type of malware, confusingly also with the acronym RAT.1I don’t know if Orcus was being cute with the name, or this is just a coincidence.
This, in combination with the sale of a DDNS (dynamic domain name server) service to hackers to allow them to communicate with RAT-infected computers, resulted in two NOVs for Revesz and Griebel2Nerd note: if you’re going to be a villain, take a hard look at your last name, put the word “Darth” in front of it, and see how it sounds. If it’s credibly somebody who would wear all black and whack at people with a lightsaber, reconsider your whole deal. resulting in $115,000 in penalties — $100,000 for developing, selling and promoting malware, and an additional $15,000 for the DDNS service.
A news story on this, from Krebs on Security, a security consultant’s site.
It’s pretty open and shut: clear evidence of what the RAT did, clear evidence of both Revesz and Griebel bragging on hacking forums about its ability to steal information and passwords.
Note that at the time this AMP was issued, it was for section 9 of CASL:
It is prohibited to aid, induce, procure or cause to be procured the doing of any act contrary to any of sections 6 to 8.
Canada’s Anti-Spam Legislation, s9
Per the NOV, an investigation was still underway to determine if the RAT actually been installed without consent on systems, which would be a violation of section 8:
8 (1) A person must not, in the course of a commercial activity, install or cause to be installed a computer program on any other person’s computer system or, having so installed or caused to be installed a computer program, cause an electronic message to be sent from that computer system, unless
(a) the person has obtained the express consent of the owner or an authorized user of the computer system and complies with subsection 11(5); or
(b) the person is acting in accordance with a court order.
Canada’s Anti-Spam Legislation, s8
…and unlock penalties up to $1,000,000.
The Orcus RAT seems to be alive and well as an open-source piece of software for jerks to try to use.
Some mysteries here:
The NOV has a February 2020 update that states that the time for response expired, so the issued AMP becomes enforceable:
Update 17 February 2020: Pursuant to section 24(1) of CASL, the deadline to make representations with respect to either the amount of the penalty or the acts or omissions constituting the alleged violations was February 3, 2020. Given that no representations were made, pursuant to section 24(2) of CASL, John Paul Revesz is deemed to have committed the violations and must pay the administrative monetary penalty as set out in the notice.
Where’s Griebel? Per this news story, he’s German, so that might be why he was dropped.
Stranger still: where’s the criminal charge?
$115,000 in penalties should be the least of Revesz and Griebel’s worries (if Griebel is still in play). Cybercrime is a thing, and the abovementioned news stories mention criminal charges filed by the RCMP. But the links in the stories to the 2019 RCMP press release go to a 404 page. It’s not a broken link; searching their news, there’s nothing for Revesz, Griebel or Orcus.3Testing the search function, by comparison, there’s 4,385 results for “Grand Falls,” which I used as a test because it was mentioned in the top story – now I’m deeply worried about what in God’s name is going on in Grand Falls.
There’s nothing in CanLII showing any court action: nothing relevant for the search terms Revesz, Griebel, or Orcus. Similarly nothing in WestLaw or Lexis.
When I hit the Wayback Machine, I can find an archive of the news release.
UPDATE: thanks to the incredible assistance and sleuthing of the Queen’s Law Library team, I have been pointed to upcoming court dates for a John Revesz. Whether or not these are related (or even the same John Revesz; no middle name here) isn’t confirmed.
The Orcus RAT was first outed as malware in July of 2016, with Revesz and Griebel posting openly about its utility to hackers. It even looks like Krebs did the heavy investigative lifting for the government.
A 30-month delay between this becoming public knowledge and action being taken to stop it by Canadian authorities – and then, seemingly only $115,000 in penalties – is worrisome. The lack of any charges – or delay in bringing charges – is worrisome.
If CASL is the only mechanism taken against a Canadian promulgating hacking tools, that’s troubling. The scope of these is CASL, and I don’t want to go too far down a rabbit hole about how cybercrime is prosecuted, but a scheme designed at its heart to deal with spam shouldn’t be our first and last line of defense against malware created and propagated here in Canada.
And – finally – the fact that this is only $15,000 more than Conley and nCrowd is an eyebrow-raiser as well. In the latter case, a very scammy cluster of shady companies sent out a lot of spam emails to try to get people to buy deal coupons of very limited utility. In this case, malware was unleashed on the Canadian public and promoted to hackers globally. The consequences of buying a bad coupon from a deals site versus giving hackers total access to your computer, which could easily extend to identity theft and all your banking information, is a huge gulf.
This doesn’t feel like a $15,000 swing to me, but that might be attributable to the fact that this is only a s9 violation and an investigation is still, per the NOV from almost four years ago, underway to see if Revesz also violated s8.
If nothing else, this has convinced me to keep my antivirus and malware checkers up to date.
Issued penalty: $115,000
Final penalty: $115,000
Total issued AMPs: $2,782,000
Total imposed AMPs/monetary penalties: $1,068,250
Differential: $ 1,713,750
September 21, 2020
What is it with not-quite-education companies in this space? Compu-Finder, Blackstone, and now a $100,000 penalty levied against OneClass, a service that connects students with user-generated study guides, lecture notes and video tutorials. Decision here, plus a press release.
This seems open and shut: OneClass sent CEMs without recipient consent, and (allegedly) installed a Chrome extension that harvested personal information including usernames and passwords on students’ computers. U of T still has a news piece up instructing students of the phishing email: in essence, it looks like it would access the user’s Blackboard class lists to send emails to all classmates inviting them to join OneClass. The U of T item also has instructions on how to remove it. As phishing goes, this is on the spammy but not super harmful end of things.
Issued penalty: $100,000
Final penalty: $100,000
Total issued AMPs: $2,882,000
Total imposed AMPs/monetary penalties: $1,168,250
Differential: $ 1,713,750
March 29, 2021 / January 4, 2022
A 2021 notice of violation and $75,000 AMP for Scott William Brewer, later reduced to $7,500 in payment in 2022.
Brewer committed violations in two categories – affiliate marketing, earning a commission from CEMs sent without consent to recruit people to an online gambling site, casinoonlinesoftware.com, and direct web marketing for his own online marketing and web business.
The CRTC apparently only investigated three of Brewer’s campaigns, topping 600K emails, despite
Corroborating information reviewed during the investigation indicated that Brewer may have been responsible for sending, causing or permitting to be sent, several million non-compliant CEMs. During a sample period in the investigation, approximately 11 million emails were sent from Brewer’s IP address over a 24 day period.
This, called a “hailstorm campaign,” prompted a press release from the CRTC claiming this as the “largest ever penalty to an individual for sending messages without consent”. Which seems odd, as Brian Conley was subject to $100,000 under vicarious liability for similar violations two years before. Key quote from the Chief Compliance and Enforcement Officer from that release:
“Spam campaigns, such as those carried out by Mr. Brewer, are disruptive to Canadians and undermine their confidence in electronic commerce. Obtaining consent is a fundamental principle of Canada’s anti-spam legislation. The penalty issued today demonstrates that individuals are just as accountable as businesses and must respect this principle.”
And then, 10 months later, it’s no longer a $75,000 penalty, but one for 10% of that amount. The final undertaking says:
Brewer cooperated with the CCEO, provided new information not previously available to the designated person, and has voluntarily agreed to resolve the CCEO’s outstanding concerns regarding compliance with the Act and the Regulations (CRTC).
And later, that the $7,500 penalty
…fully and completely resolves all outstanding issues between the Commission and Scott William Brewer with respect to his compliance with the Act and the Regulations (CRTC) in relation to the CCEO’s investigation into the sending of CEMs during the period of 1 December 2015 to 23 May 2018 and up to the effective date of this undertaking.
Scott seems to be doing fine, with a business pivot to site-building for SEO and sales conversions, per his LinkedIn profile.
Issued penalty: $75,000
Final penalty: $7,500
Total issued AMPs: $2,957,000
Total imposed AMPs/monetary penalties: $1,175,750
Differential: $ 1,781,250
December 6, 2021
A $200,000 imposed AMP to the Gap, for a marketing campaign including its subsidiaries Banana Republic and Old Navy – CEMs without consent and without an unsubscribe mechanism.
Gap seems to have agreed with the CCEO, agreed to pay, and implement a compliance program.
No specifics in the NOV, unlike previous decisions that articulated a number of campaigns or messages; here’s the decision in full:
Undertaking: Gap Inc.
File No.: 9110-2021-00605
Effective date of undertaking: 6 December 2021
Monetary payment amount: $200,000
Under section 21 of An Act to promote the efficiency and adaptability of the Canadian economy by regulating certain activities that discourage reliance on electronic means of carrying out commercial activities, and to amend the Canadian Radio-television and Telecommunications Commission Act, the Competition Act, the Personal Information Protection and Electronic Documents Act and the Telecommunications Act, S.C. 2010, C. 23 (CASL, or the Act)
Person entering into an undertaking
Gap Inc.
Acts and omissions covered by the undertaking and provisions at issue
Gap Inc. has voluntarily entered into an undertaking with the Chief Compliance and Enforcement Officer (CCEO) concerning alleged violations of paragraphs 6(1)(a) and 6(2)(c) and subsections 11(1) and 11(3) of the Act.
Following an investigation, the CCEO alleged that commercial electronic messages (CEMs) were sent or caused to be sent by Gap Inc., between 7 January 2018 and 11 August 2021 to promote sales for Gap Inc. as well as for subsidiaries Banana Republic and Old Navy, without consent from recipients and/or not including an unsubscribe mechanism which could readily be performed,.
Amount owing and summary of other conditions
During the course of the investigation, Gap Inc. has cooperated with the CCEO. Gap Inc. has voluntarily undertaken, pursuant to section 21 of the Act, to resolve the CCEO’s outstanding concerns regarding Gap Inc.’s compliance with the Act and the Electronic Commerce Protection Regulations (CRTC), SOR/2012-36 (the Regulations (CRTC)), including undertaking to comply with, and ensuring that any third party authorized to send a CEM complies with the Act and Regulations (CRTC).
As part of this undertaking, Gap Inc. agreed to make a monetary payment of $200,000 to the Receiver General for Canada in accordance with subsection 28(3) of the Act.
In addition to the monetary payment, and in order to promote compliance with the Act and the Regulations (CRTC), Gap Inc. undertakes to update its compliance program addressing the sending of CEMs. This compliance program has included or will include:
corporate compliance policies and procedures;
training and education for employees of Gap Inc.; and,
monitoring, auditing and reporting mechanisms.
In addition, Gap Inc. will monitor and review its policies and procedures to determine whether any have the effect of providing incentives for employees to violate the Act and the Regulations (CRTC) and, if so, Gap Inc. undertakes to eliminate such incentives.
Gap Inc. will also develop and provide periodic training programs, which include compliance procedures and processes to comply with Act, for employees involved with commercial electronic messages and related compliance.
Finally, Gap Inc. will register and track CEM complaints and the subsequent resolution of those complaints. Gap Inc. will also implement effective corrective measures for compliance failures and within six months of the effective date of the undertaking will supplement the information it has already provided to the CCEO of the corrective measures already implemented to date, as well as information supporting any updates to its Compliance Program.
This undertaking fully and completely resolves all outstanding issues between the Commission and Gap Inc. with respect to Gap Inc.’s compliance with the Act and the Regulations (CRTC) in relation to the CCEO’s investigation into the sending of CEMs for the period up to and including the effective date of this undertaking.
Straightforward.
And here, for the last time (as of August 2023, with the Brewer decision in 2022 being the final one reported4UPDATE: This is no longer true; there is a July 2023 AMP, reported in late October 2023: 18 months since the last reported CASL enforcement decision, which is the longest gap in its history.), is the tally:
Issued penalty: $200,000
Final penalty: $200,000
Total issued AMPs: $3,157,000
Total imposed AMPs/monetary penalties: $1,375,750
Differential: $ 1,781,250
The difference between the imposed and issued penalties is greater than the penalties imposed, which is interesting.
A quick stop off with a relatively recent NOV, and then we’ll sum all this up.
This is part eight of a multi-part series reviewing Canada’s Anti-Spam Legislation in practice since its introduction in 2014 and the beginnings of enforcement in 2015. Crosslinks will be added as new parts go up.
Part 1: Terminology
Part 4: Case File – Compu-Finder
Part 5: Case File Anthology, 2015-2016
Part 6: Case File – Blackstone Education
Part 7: Case File Anthology, 2017-2018
Part 8: Case File – Brian Conley/nCrowd
Part 9: Case File Anthology, 2019-2022
Core resources:
Enforcement Actions Table (CASL selected)
In April 2019, a $100,000 decision was imposed on Brian Conley (as an individual) for violations committed by the company he was CEO of, nCrowd, in a pair of identically dated decisions: first, a NOV, and second, a compliance and enforcement decision, both from April 23, 2019. You’ll recall this from our 2015-16 anthology post, where we saw the AMP issued (but not imposed) in December of 2016.1Confusingly, in the table of enforcement actions, the 2016 Brian Conley entry doesn’t link to the issued AMP, but directly to the 2019 decision, so we can’t see the issued notice, only the final decisions.
This is the first time vicarious liability has been named in a decision: “Background,” final paragraph:
As a result of the circumstances cited above, specifically the fact that the companies involved were operational then dissolved or otherwise ended, any enforcement actions directed towards such companies would have no deterrent effect nor effectively promote compliance. Therefore, Commission staff pursued the corporate directors through vicarious liability in order to encourage future compliance with the Act.
It’s also in the title of the NOV itself, “Notice of Violation: Investigation into non-compliant emails sent by Couch Commerce Inc. and nCrowd, Inc. including the vicarious liability of corporate directors.”
Vicarious liability is part of the Act, as is the responsibility of directors and officers, in [s31-32] of the Act:
Directors, officers, etc., of corporations
31 An officer, director, agent or mandatary of a corporation that commits a violation is liable for the violation if they directed, authorized, assented to, acquiesced in or participated in the commission of the violation, whether or not the corporation is proceeded against.2Note the “whether or not” here — in theory, although it hasn’t happened yet, the CRTC could double-dip with both an institution and an individual being liable. Also — this is past the limit of my understanding, but this only applying to “corporations” seems unnecessarily narrow, but there may be a legal definition of “corporation” that differs from my understanding of the word.
Vicarious liability
32 A person is liable for a violation that is committed by their employee acting within the scope of their employment or their agent or mandatary acting within the scope of their authority, whether or not the employee, agent or mandatary is identified or proceeded against.3See above note re. this allowing the CRTC to penalize individuals across management and labour tiers.
And if the name Couch Commerce seems familiar, it should – these Couch Commerce investigations resulted in an earlier NOV against Ghassan Halazon (“in his individual capacity”) in 2017, as covered in our 2017-2018 anthology. The CRTC states in its September 2019 Activity Summary that this is its first vicarious liability finding. Halazon was the first finding to be resolved, but remember that Conley was first issued the AMP in December of 2016, prior to Halazon being penalized.
But nCrowd and Couch Commerce were only the tip of a massive, scammy iceberg: the web of companies connected to those two (and many, many brand names as well) was extensive, and kudos to whoever put the leg work in to pull it all together, resulting in this truly impressive chart that accompanies the NOV:
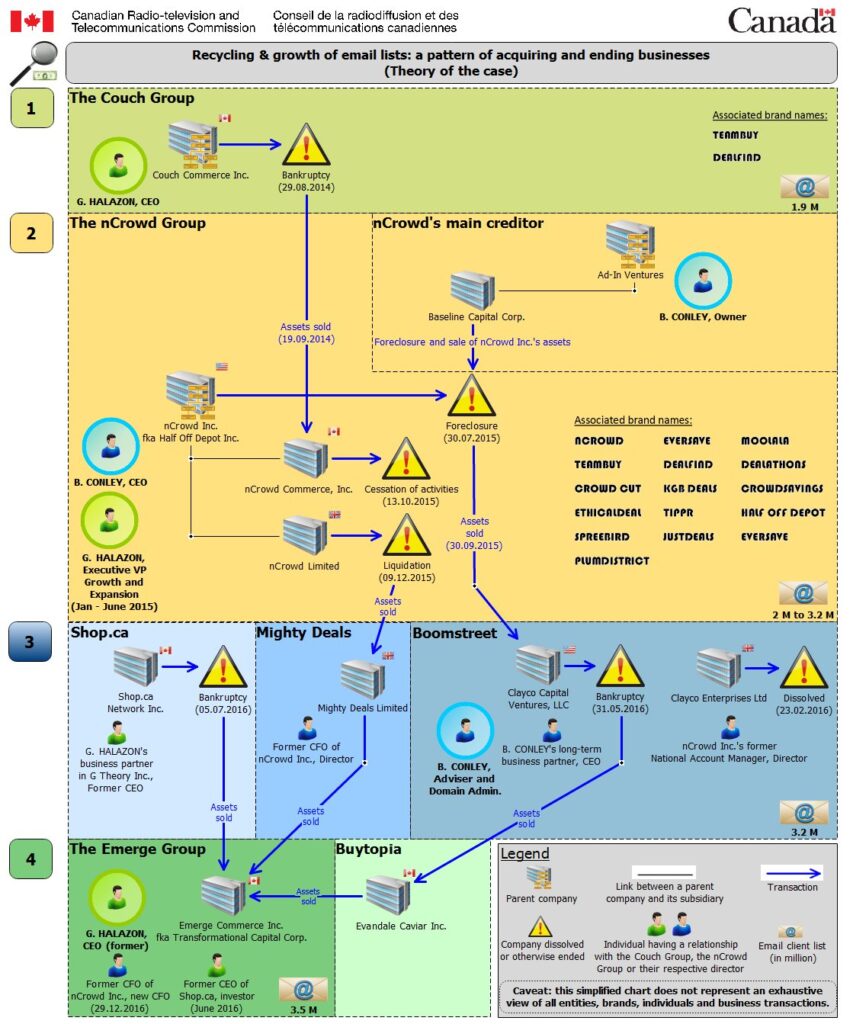
While the graphic design may be questionable, it’s quite a labyrinth of companies.
Where it lands is almost 3.5 million email addresses promoting what the CRTC doesn’t call, but I feel pretty free in describing, as a massive series of bait-and-switch deal scams; from the “Background” section of the NOV:
The key assets acquired in the chain of transactions listed in the chart were intangible, essentially the email distribution list, domain names and trademarks. These ownership changes allowed a new company to continue on the business with an ever larger email distribution list without the assumed liabilities of the former company. However, the continuity of service was damaged: as merchants ceased being paid for their products, they refused to ship products ordered by customers. As a result, both merchants and customers ended up losing money, since the voucher business closed or entered into bankruptcy proceedings before merchants and customers were fully compensated for their transactions.
Since these companies seem to launch and disappear rapidly (see the diagram above), the vicarious/director liability makes perfect sense. Tracking the person or people responsible, rather than the corporate entity, keeps the legislation viable when you’re dealing with MBAs who are shuttling through companies like three-card monte.
What’s not clear is how this is decided – why is Conley (and previously, Halazon) selected here, but in other instances, companies (Kellogg, Blackstone) are the recipients?
I have so many questions after seeing how Conley and Halazon, and nCrowd and Couch, are almost symbiotic through the life of these companies, their practically identical infractions, and the literally fractional penalty levied against Halazon as compared to Conley. Halazon was the executive vice-president of nCrowd while Conely was the CEO, for Pete’s sake.
In the Halazon NOV:
The investigation alleged that commercial electronic messages (CEMs) were sent or caused or permitted to be sent by Couch Commerce to recipients without a compliant unsubscribe mechanism during the period of 2 July 2014 to 9 September 2014, while Mr. Halazon was CEO of Couch Commerce. More specifically, it was alleged that the unsubscribe mechanism did not function, or could not be readily performed, or unsubscribe requests were not given effect until more than 10 business days after a request has been sent. It was also alleged that Mr. Halazon was personally liable for this violation pursuant to section 31 of the Act. 4Undertaking: Mr. Halazon and TCC; “Acts and omissions covered by the undertaking and provisions at issue,” para. 2
In the Conley NOV:
Commission staff alleged and the Commission found in Decision 2019-111 that between 25 September 2014 and 1 May 2015, nCrowd, Inc. sent CEMs or caused or permitted any of its subsidiaries, namely nCrowd Commerce, Inc. and nCrowd Limited, to send CEMs to electronic addresses, without consent and without a functioning unsubscribe mechanism contrary to paragraphs 6(1)(a) and 6(2)(c) of the Act.
Commission staff also alleged and the Commission found in Decision 2019-111 that Brian Conley acquiesced in these violations, while he was the President and Chief Executive Officer (CEO) of the nCrowd companies. As CEO, Brian Conley took no action and turned a blind eye to the practices being employed at his companies in terms of the acquisition and use of email distribution lists, despite the fact that in this line of business, an email distribution list is one of the most important assets through which to generate revenues. Protecting such an asset, including ensuring continued ability to use it, under CASL, should therefore have been important to the nCrowd group and its CEO. However, the nCrowd group’s email distribution and consent-tracking lists were largely inaccurate, incomplete, and altered.
There’s clearly a gap there – Halazon/Couch doesn’t seem to have a problem with consent (or at least, consent goes unremarked on in the decision). Conley/nCrowd was clearly lying about consent, while having arguably identical unsubscribe issues. The email volume attributed to Couch Group (1.9M) and stated above for nCrowd (1.9M) seems to be the same.
Is this a $90,000 gap? The CRTC seems to think so.
This underscores one of the things I find unsettling about CASL: “The maximum penalty for a violation is $1,000,000 in the case of an individual, and $10,000,000 in the case of any other person.” [Act, s20(4)] But under that (to date never imposed) threshold, the purpose of the penalty is “to promote compliance with this Act and not to punish,” and factors for penalty are broad and very discretionary, and rely as much on comportment and ability to pay as they do on what is actually done in violation of the Act:
Purpose of penalty
(2) The purpose of a penalty is to promote compliance with this Act and not to punish.
Factors for penalty
(3) The following factors must be taken into account when determining the amount of a penalty:
(a) the purpose of the penalty;
(b) the nature and scope of the violation;
(c) the person’s history with respect to any previous violation under this Act, any previous conduct that is reviewable under section 74.011 of the Competition Act and any previous contravention of section 5 of the Personal Information Protection and Electronic Documents Act that relates to a collection or use described in subsection 7.1(2) or (3) of that Act;
(d) the person’s history with respect to any previous undertaking entered into under subsection 21(1) and any previous consent agreement signed under subsection 74.12(1) of the Competition Act that relates to acts or omissions that constitute conduct that is reviewable under section 74.011 of that Act;
(e) any financial benefit that the person obtained from the commission of the violation;
(f) the person’s ability to pay the penalty;
(g) whether the person has voluntarily paid compensation to a person affected by the violation;
(h) the factors established by the regulations; and
(i) any other relevant factor.
Philosophically, I understand this. But in practice, this results in published decisions that have such big swings, with no share information as to why, that it makes the entire scheme seem very arbitrary in its application and enforcement.
Which may be a feature and not a bug – I’ll address that in my wrap-up.
Issued penalty: $100,000
Final penalty: $100,000
Total issued AMPs: $2,667,000
Total imposed AMPs/monetary penalties: $953,250
Differential: $ 1,713,750
Up next: the 2019-2022 anthology. Technically there’s only one 2019 decision after Conley, and it’s only the issuing and not imposition of an AMP, so this will be a smidge broader than the previous anthologies.